Be a part of high executives in San Francisco on July 11-12, to listen to how leaders are integrating and optimizing AI investments for achievement. Learn More
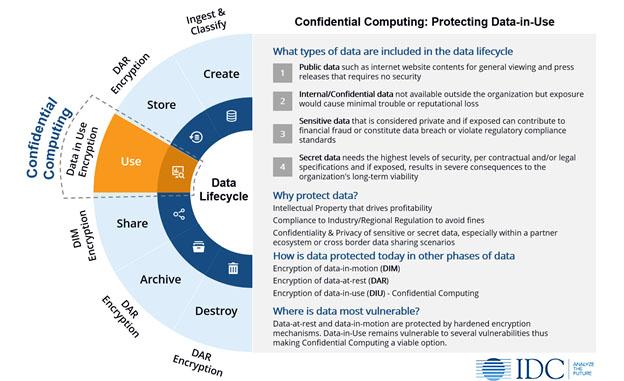
For enterprises to appreciate the potential that real-time datasets can ship, cloud tech stacks want hardening with zero belief. On this, confidential computing is crucial to securing knowledge at relaxation, in transit and in use.
VentureBeat spoke with CIOs from banking, monetary companies and insurance coverage industries who say they’re at numerous levels of piloting confidential computing to see how nicely it handles their compliance, regulatory reporting and real-time auditing of knowledge transactions. Notably, compliance and assist for zero belief frameworks are rising because the killer apps.
One CIO who spoke on situation of anonymity mentioned that their board of administrators’ crew assigned to threat administration needs to see proof that knowledge is secured throughout use inside protected CPU enclaves and Trusted Execution Environments (TEEs), two foundational components of confidential computing.
Board members on threat administration groups recall Meltdown and Spectre vulnerabilities that concentrate on processors that depend on department prediction and superior speculative actions. CIOs and CISOs say boards must see pilot knowledge and simulated assaults thwarted earlier than they go into manufacturing with confidential computing.
Primarily based on interval pilots that VentureBeat is briefed on, it’s clear that confidential computing strengthens zero belief in multicloud tech stacks on which extremely regulated companies depend on. Compliance, privateness, and safety use instances, notably on public cloud, have gained probably the most important traction, accounting for 30 to 35% of the worldwide market, in line with Everest Teams’ report Confidential Computing: The Subsequent Frontier in Information Safety. And, the confidential computing market is predicted to develop to $54 billion by 2026.

What’s confidential computing?
Confidential Computing is a cloud computing expertise that secures knowledge throughout processing by isolating delicate knowledge in a protected CPU enclave. The contents of each enclave, together with the information and evaluation methods, are solely accessed with licensed programming codes, remaining invisible and protected against exterior entry.
Confidential computing is gaining momentum as a result of it offers better knowledge confidentiality, knowledge and code integrity than present safety applied sciences defending cloud tech stacks and infrastructure.
The Confidential Computing Consortium (CCC) is instrumental in selling and defining confidential computing throughout the trade. The CCC is a Linux Basis undertaking that mixes the efforts of {hardware} distributors, cloud suppliers and software program builders to assist improve the adoption and standardization of TEE applied sciences.
TEEs defend proprietary enterprise logic, analytics features, machine studying (ML) algorithms and purposes. Founding members embody Alibaba, Arm, Google, Huawei, Intel, Microsoft and Crimson Hat. The CCC defines confidential computing as defending knowledge in use by computing in a hardware-based TEE.

Compliance a development driver
What’s working in confidential computing’s favor with boards is how efficient it’s at making certain regulatory compliance. It’s additionally confirmed to be efficient at implementing end-to-end safety and least privileged entry to knowledge at relaxation, in transit and in use. CIOs and CISOs inform VentureBeat that they count on confidential computing to be complimentary to their Zero Belief Community Entry (ZTNA) frameworks and supporting initiatives.
John Kindervag created zero belief and at present serves as SVP for cybersecurity technique and is a bunch fellow at ON2IT Cybersecurity. He’s additionally an advisory board member for a number of organizations, together with to the places of work of the CEO and president of the Cloud Security Alliance.
He not too long ago instructed VentureBeat that “the largest and best-unintended consequence of zero belief was how a lot it improves the flexibility to take care of compliance and auditors.” And, he mentioned {that a} Forrester consumer referred to as and knowledgeable him how completely aligned zero belief was with their compliance and audit automation course of.
Securing cloud tech stacks with confidential computing
Mark Russinovich, CTO and technical fellow of Microsoft Azure writes that: “Our imaginative and prescient is to remodel the Azure cloud into the Azure confidential cloud, transferring from computing within the clear to computing confidentially throughout the cloud and edge. We need to empower prospects to realize the best ranges of privateness and safety for all their workloads.”
Cloud platform suppliers endorsed and started integrating CCC’s necessities into their product roadmaps as early as 2019, when the CC was fashioned. What’s guiding cloud platform suppliers is the purpose of offering their prospects with the technical controls essential to isolate knowledge from cloud platform operators, their operators, or each.
Microsoft’s Azure confidential computing is taken into account an trade chief as a result of their DevOps groups designed the platform to transcend hypervisor isolation between buyer tenants to safeguard buyer knowledge from Microsoft operator entry.
CIOs and CISOs have recognized to VentureBeat what they’re on the lookout for relating to a baseline stage of efficiency with confidential computing. First, remote attestation must be confirmed in dwell buyer websites with referenceable accounts prepared to talk to how they’re utilizing it to test the integrity of the surroundings. Second, trusted launch workflows and processes ideally must be cloud-based, in manufacturing, and confirmed to validate digital machines beginning up with licensed software program and steady distant attestation to test for patrons.
Silicon-based zero belief is the way in which
Martin G. Dixon, Intel fellow and VP of Intel’s safety structure and engineering group writes that, “I imagine the zero belief ideas shouldn’t cease on the community or system. Slightly, they are often utilized down contained in the silicon. We even seek advice from infrastructure on the chip as a community or ‘community on a chip.’”
A part of that imaginative and prescient at Intel included the necessity for attestation to grow to be extra pervasive and moveable to gas confidential computing’s development, beginning on the silicon stage.
To handle this, the corporate launched Project Amber, whose objectives embody offering unbiased attestation, extra uniform, moveable attestation and improved coverage verification.
“With the introduction of Challenge Amber, Intel is taking confidential computing to the following stage in our dedication to a zero belief method to attestation and the verification of compute belongings on the community, edge and within the cloud,” Greg Lavender, Intel’s CTO mentioned on the firm’s Intel Vision conference final yr.
He continued that Intel is targeted on “extending attestation companies within the cloud knowledge heart within the edge computing environments to supply unprecedented safety. The Intel Software program as a Service providing Challenge Amber is a trusted service resolution that may present organizations with unbiased verification and trustworthiness of buyer belongings regardless of the place they run.”

Getting silicon-based zero belief safety proper wants to start out with TEEs hardened sufficient to guard delicate knowledge at relaxation, in transit and in use. Migrating zero belief into silicon additionally strengthens authentication and authorization, taking identification and entry administration (IAM) and privileged entry administration to the {hardware} stage, which makes it tougher for attackers to bypass or manipulate authentication techniques and improves the safety of confidential computing environments.
Extra advantages of transferring zero belief into silicon embody encrypting all knowledge and making certain the next stage of knowledge integrity and making use of zero belief rules to knowledge encryption and authentication. With zero belief frameworks requiring steady safety configuration and posture validation for all customers and gadgets, supporting monitoring in silicon will scale back the overhead on cloud platform efficiency.