Head over to our on-demand library to view classes from VB Rework 2023. Register Right here
Exploiting gaps in cloud infrastructure which are leaving endpoints, identities and microservices uncovered is a fast method for an attacker to steal credentials and infect an enterprise’s DevOps course of. Assaults to use such gaps are skyrocketing.
The current 2023 Thales Cloud Security Study gives laborious numbers: 39% of enterprises have been hit with an information breach beginning of their cloud infrastructure this yr alone. A complete of 75% of enterprises say that greater than 40% of the info they retailer within the cloud is delicate. Lower than half of that information is encrypted.
CrowdStrike’s 2023 Global Threat Report explains why cloud-first assaults are rising: Attackers are transferring away from deactivating antivirus, firewall applied sciences and log-tampering efforts and towards modifying core authentication processes, together with rapidly gaining credentials and identity-based privileges.
The attackers’ objective is to steal as many identities and privileged entry credentials as attainable to allow them to turn into access brokers — promoting stolen identification data in bulk at excessive costs on the darkish internet. Entry brokers and the brokerages they’re creating usually flip into profitable, fast-growing unlawful companies. CrowdStrike’s report discovered greater than 2,500 ads for entry brokers providing stolen credentials and identities on the market.
What’s driving CNAPP adoption
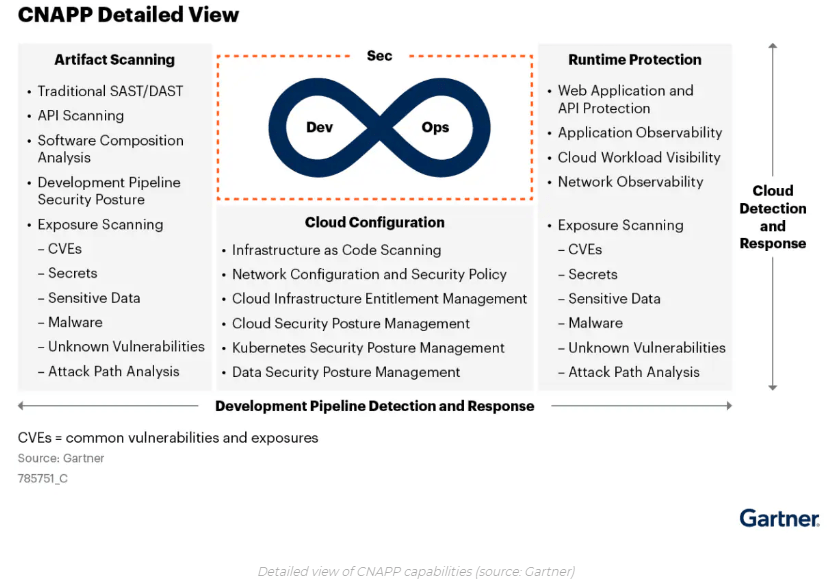
Consolidating tech stacks continues to dominate CISOs’ plans, pushed by the necessity to enhance efficacy, handle a extra numerous multicloud safety posture, shut gaps between cloud apps and shift safety left in DevOps pipelines. All these components are contributing to the rising adoption of cloud-native application protection platforms (CNAPP).
“CNAPPs are fashioned from the convergence of cloud safety posture administration (CSPM) and cloud workload safety platform (CWPP) capabilities in addition to different safety tooling like entitlement administration, API controls and Kubernetes posture management,” reads Gartner’s 2023 Planning Guide for Security.

Main CNAPP distributors are competing in varied areas, crucial of which embrace the efficacy of their cloud infrastructure entitlement administration (CIEM), Kubernetes safety, API controls and cloud detection and response (CDR), in accordance with CISOs VentureBeat spoke with. Demand for CNAPP is biggest in bigger enterprises from extremely regulated industries that depend on in depth multicloud configurations. Finance, authorities and healthcare suppliers are among the many most dominant industries.
CISOs inform VentureBeat that one of the vital sensible advantages of CNAPPs is the chance to consolidate legacy instruments with restricted visibility throughout all menace surfaces and endpoints. The takeaway? Lowering software sprawl is a fast win.
Benchmarking the highest 20 CNAPP platforms for 2023
Full-platform CNAPP distributors present built-in cloud-native safety platforms starting from DevOps to manufacturing environments. Listed here are the highest 20 platforms of 2023:
Aqua Security: Extremely regarded for its method of scanning container registries and pictures, CSPM and runtime safety for container and cloud-native safety. Additionally has full life cycle safety and superior runtime strategies, together with help for the prolonged Berkeley Packet Filter (eBPF).
Check Point: Offers a broad set of capabilities by its CloudGuard platform, together with CSPM, CIEM and superior runtime safety. Recognized for securing cloud workloads throughout environments with identity-centric entry controls, in addition to menace intelligence integration to supply real-time contextual prioritization of dangers.
Cisco: Just lately acquired Lightspin for its Kubernetes safety capabilities and CSPM. Its Tetration platform focuses on runtime safety, leveraging eBPF and third-party insights for superior container monitoring and granular controls. Cisco emphasizes behavioral analytics to detect anomalies and threats in container environments and gives robust controls to restrict lateral motion between workloads.
CrowdStrike: Affords a number one CNAPP suite emphasizing identity-centric visibility, least-privilege enforcement and steady monitoring. Its runtime safety leverages brokers and eBPF for workload safety. CrowdStrike’s key design objectives included imposing least-privileged entry to clouds and offering steady detection and remediation of identification threats.
Cybereason: Platform focuses closely on malicious conduct detection. A core power is its potential to detect threats utilizing behavior-based strategies. The corporate can also be recognized for API integrations, AI and machine studying (ML) experience. Cybereason makes a speciality of detecting compromised accounts and insider threats through detailed person exercise monitoring.
Juniper Networks: Collects in depth information on machine posture and site visitors patterns to supply networking context for safety insights. Additionally allows segmentation controls between Juniper units.
Lacework: Centered on workload conduct evaluation for containers and runtime strategies resembling eBPF to realize a complete perception into container exercise and efficiency. Its emphasis on detecting anomalies utilizing superior ML algorithms which are custom-tuned for containerized environments is a key differentiator.
Microsoft: Integrates safety throughout Azure providers with zero-trust controls, enforces least-privileged entry and gives workload protections resembling antivirus and firewalls. Makes use of Microsoft Graph to correlate safety analytics and occasions throughout Azure.
Orca Security: Performs steady authorization checks on identities and entitlements throughout cloud environments. A key differentiator is the power to generate detailed interactive maps that visualize relationships between cloud property, customers, roles and permissions.
Palo Alto Networks Prisma Cloud: Offers a broad suite of capabilities, together with identity-based microsegmentation and sturdy runtime safety with eBPF. Prisma Cloud is an trade chief recognized for superior protections resembling deception method and consists of in depth compliance automation and DevSecOps integrations.
Qualys: Focuses on compliance and vulnerability administration by steady scanning and least-privilege controls. Identifies vulnerabilities all through the life cycle and allows automated patching and remediation workflows. One other key differentiator is compliance mapping and reporting.
Rapid7: Enforces least privilege entry and allows automated response and remediation triggered by occasions. Affords pre configured insurance policies and streamlined workflows designed for small safety groups. An intuitive person interface and speedy implementation purpose to simplify deployment and value for organizations with restricted safety sources.
Sonrai Security: Focuses on entitlement administration and identity-based safety utilizing graph database expertise to find and map person identities throughout cloud environments. Consumer identification, geolocation and different contextual components can outline {custom} entry controls.
Sophos: Focuses on information safety, compliance and menace monitoring capabilities and presents superior information loss prevention resembling file fingerprinting and optical character recognition. Cloud environments even have anti-ransomware protections.
Sysdig: Centered on runtime safety and superior behavioral monitoring. For container-level visibility and anomaly detection, the platform makes use of embedded brokers. Sysdig Safe Advisor consists of an built-in safety assistant to assist SecOps and IT groups create insurance policies sooner.
Tenable: Centered on compliance, entitlement administration and identification governance. Affords complete compliance automation mapped to PCI, HIPAA and ISO rules. Additionally gives differentiated identification and compliance administration by superior capabilities to implement least privilege and certify entry.
Trend Micro: Contains runtime safety, compliance and menace monitoring, enforces insurance policies and protects cloud environments from file- and email-based threats. Customized sandboxing for suspicious file evaluation can also be included.
Uptycs: Differentiates itself by combining CNAPP capabilities with prolonged detection and response (EDR) capabilities. Employs information lake strategies to retailer and correlate safety telemetry throughout cloud and container workloads. Threats are recognized utilizing behavioral analytics, and automatic response workflows permit for speedy remediation.
Wiz: Centered on steady entry controls, micro segmentation and identity-based adaptive safety. Robotically discovers and visualizes relationships between cloud property, customers and permissions. Wiz additionally conducts danger evaluation to establish potential assault paths and stands out with its specialised visualization, identification administration and micro-segmentation.
Zscaler: Posture Control prioritizes dangers attributable to misconfigurations, threats and vulnerabilities. Fully agentless and correlates information from a number of safety engines.
Why CNAPP will succeed as a consolidation catalyst
CNAPPs are gaining recognition as CISOs look to consolidate and strengthen their safety expertise stacks. Platforms can present built-in safety throughout the event lifecycle and cloud environments by combining capabilities together with cloud workload safety, container safety and CIEM.
CNAPP adoption will proceed accelerating in extremely regulated industries together with finance, authorities and healthcare. CISOs in these industries are underneath strain to consolidate tech stacks, enhance compliance and safe advanced cloud infrastructure concurrently. As a result of they supply a unified platform that meets a number of safety and compliance necessities, CNAPPs are proving to be an efficient consolidation catalyst.