Be a part of prime executives in San Francisco on July 11-12, to listen to how leaders are integrating and optimizing AI investments for fulfillment. Learn More
Cyberattacks exploiting gaps in cloud infrastructure — to steal credentials, identities and information — skyrocketed in 2022, rising 95%, with instances involving “cloud-conscious” menace actors tripling year-over-year. That’s in response to CrowdStrike’s 2023 Global Threat Report.
The report finds dangerous actors shifting away from deactivation of antivirus and firewall applied sciences, and from log-tampering efforts, searching for as an alternative to “modify authentication processes and assault identities,” it concludes.
As we speak, identities are below siege throughout an unlimited threatscape. Why are identities and privileged entry credentials the first targets? It’s as a result of attackers need to turn into access brokers and promote pilfered data in bulk at excessive costs on the darkish net.
CrowdStrike’s report offers a sobering have a look at how rapidly attackers are reinventing themselves as entry brokers, and the way their ranks are rising. The report discovered a 20% improve within the variety of adversaries pursuing cloud information theft and extortion campaigns, and the largest-ever improve in numbers of adversaries — 33 new ones present in only a 12 months. Prolific Scattered Spider and Slippery Spider attackers are behind many recent high-profile attacks on telecommunications, BPO and know-how firms.
Assaults are setting new velocity information
Attackers are digitally remodeling themselves sooner than enterprises can sustain, rapidly re-weaponizing and re-exploiting vulnerabilities. CrowdStrike discovered menace actors circumventing patches and sidestepping mitigations all year long.
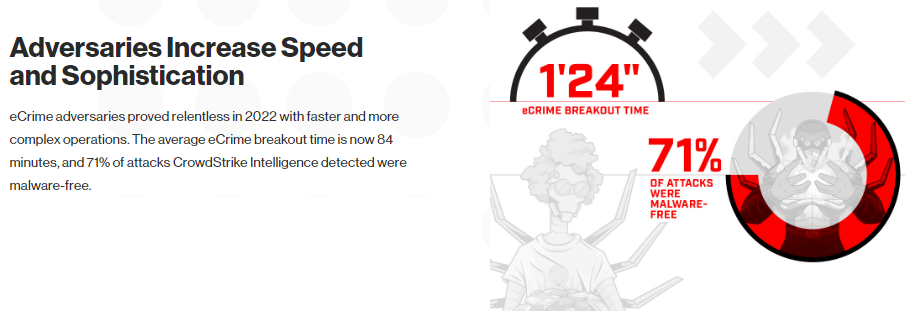
The report states that “the CrowdStrikeFalcon OverWatch staff measures breakout time — the time an adversary takes to maneuver laterally, from an initially compromised host to a different host inside the sufferer setting. The common breakout time for interactive eCrime intrusion exercise declined from 98 minutes in 2021 to 84 minutes in 2022.”
CISOs and their groups want to reply extra rapidly, because the breakout time window shortens, to reduce prices and ancillary damages attributable to attackers. CrowdStrikes advises safety groups to fulfill the 1-10-60 rule: detecting threats inside the first minute, understanding the threats inside 10 minutes, and responding inside 60 minutes.

Entry brokers make stolen identities into finest sellers
Entry brokers are making a thriving enterprise on the darkish net, the place they market stolen credentials and identities to ransomware attackers in bulk. CrowdStrike’s extremely regarded Intelligence Team discovered that authorities, monetary companies, and industrial and engineering organizations had the best common asking worth for entry. Entry to the educational sector had a mean worth of $3,827, whereas the federal government had a mean worth of $6,151.
As they provide bulk offers on lots of to hundreds of stolen identities and privileged-access credentials, entry brokers are utilizing the “one-access one-auction” approach, in response to CrowdStrike’s Intelligence Staff. The staff writes, “Entry strategies utilized by brokers have remained comparatively constant since 2021. A prevalent tactic entails abusing compromised credentials that have been acquired through data stealers or bought in log retailers on the felony underground.”
Entry brokers and the brokerages they’ve created are booming unlawful companies. The report discovered greater than 2,500 ads for entry brokers providing stolen credentials and identities on the market. That’s a 112% improve from 2021.
CrowdStrike’s Intelligence Staff authors the report primarily based on an evaluation of the trillions of day by day occasions gathered from the CrowdStrike Falcon platform, and insights from CrowdStrike Falcon OverWatch.
The findings amplify earlier findings from CrowdStrike’s Falcon OverWatch threat hunting report that discovered attackers, cybercriminal gangs and advanced persistent threats (APTs) are shifting to the malware-free intrusion exercise that accounts for as much as 71% of all detections listed within the CrowdStrike threat graph.

Cloud infrastructure assaults beginning on the endpoint
Proof continues to point out cloud computing rising because the playground for dangerous actors. Cloud exploitation grew by 95%, and the variety of instances involving ”cloud-conscious” menace actors almost tripled year-over-year, by CrowdStrike’s measures.
“There may be rising proof that adversaries are rising extra assured leveraging conventional endpoints to pivot to cloud infrastructure,” wrote the CrowdStrike Intelligence Staff, signaling a shift in assault methods from the previous. The report continues, “the reverse can also be true: The cloud infrastructure is getting used as a gateway to conventional endpoints.”
As soon as an endpoint has been compromised, attackers usually go after the center of a cybersecurity tech stack, beginning with identities and privileged entry credentials and eradicating account entry. They usually then transfer on to information destruction, useful resource deletion and repair interruption or destruction.
Attackers are re-weaponizing and re-exploiting vulnerabilities, beginning with CVE-2022-29464, which allows distant code execution and unrestricted file uploads. On the identical day that the vulnerability affecting a number of WSO2 merchandise was disclosed, the exploit code was publicly accessible. Adversaries have been fast to capitalize on the chance.
Falcon OverWatch threat hunters started figuring out a number of exploitation incidents by which adversaries make use of infrastructure-oriented techniques, strategies and procedures (TTPs) according to China-nexus exercise. The Falcon OverWatch staff found that attackers are pivoting to utilizing profitable cloud breaches to establish and compromise conventional IT belongings.

CrowdStrike doubles down on CNAPP
Aggressive parity with attackers is elusive and short-lived in cloud safety. All of the main cybersecurity suppliers are effectively conscious of how briskly attackers can innovate, from Palo Alto Networks saying how invaluable assault information is to innovation to Mandiant’s founder and CEO warning that attackers will out-innovate a safe enterprise by relentlessly learning it for months.
No gross sales name or govt presentation to a CISO is full and not using a name for higher cloud safety posture administration and a extra sensible strategy to identification and entry administration (IAM), improved cloud infrastructure entitlement administration (CIEM) and the prospect to consolidate tech stacks whereas bettering visibility and decreasing prices.
These components and extra drove CrowdStrike to fast-track the enlargement of its cloud native software safety platform (CNAPP) in time for its Fal.Con buyer occasion in 2022. The corporate isn’t alone right here. A number of main cybersecurity distributors have taken on the bold aim of bettering their CNAPP capabilities to maintain tempo with enterprises’ new complexity of multicloud configurations. Distributors with CNAPP on their roadmaps embody Aqua Security, CrowdStrike, Lacework, Orca Security, Palo Alto Networks, Rapid7 and Trend Micro.
For CrowdStrike, the highway forward depends on an assortment of modern tooling.
“One of many areas we’ve pioneered is that we are able to take weak indicators from throughout completely different endpoints. And we are able to hyperlink these collectively to seek out novel detections,” CrowdStrike co-founder and CEO George Kurtz advised the keynote viewers on the firm’s annual Fal.Con occasion final 12 months.
“We’re now extending that to our third-party companions in order that we are able to have a look at different weak indicators throughout not solely endpoints however throughout domains and provide you with a novel detection,” he mentioned.
What’s noteworthy in regards to the improvement is how the CrowdStrike DevOps and engineering groups added new CNAPP capabilities for CrowdStrike Cloud Security whereas additionally together with new CIEM options and the combination of CrowdStrike Asset Graph. Amol Kulkarni, chief product and engineering officer, advised VentureBeat that CrowdStrike Asset Graph offers cloud asset visualization and defined how CIEM and CNAPP may also help cybersecurity groups see and safe cloud identities and entitlements.
Kulkarni has set a aim of optimizing cloud implementations and performing real-time level queries for speedy response. Which means combining Asset Graph with CIEM to allow broader analytical queries for asset administration and safety posture optimization. At a convention final 12 months, he demonstrated how such tooling can present full visibility of assaults and routinely stop threats in actual time.
CrowdStrike’s key design targets included implementing least-privileged entry to clouds and offering steady detection and remediation of identification threats. Scott Fanning, senior director of product administration, cloud safety at CrowdStrike, advised VentureBeat that the aim is to stop identity-based threats ensuing from improperly configured cloud entitlements throughout a number of public cloud service suppliers.