Head over to our on-demand library to view periods from VB Remodel 2023. Register Right here
Utilizing generative AI to automate scripts in search of unprotected endpoints, ports and infrastructure safety gaps, cybercrime gangs provide bounties for focused organizations’ worker digital gadget passwords and identities. As many latest assaults present, placing any belief in identities is a breach ready to occur.
Notably, digital and bodily crime in healthcare has lengthy been converging and rising right into a pandemic. Healthcare suppliers warn their staff to not go away their laptops in their cars unattended. The Coplin Well being incident wherein 43,000 records containing personal health information (PHI) have been compromised after an worker’s laptop computer was stolen from their automobile remains to be a priority boards point out relating to id safety. A stolen laptop computer with unencrypted PHI information can typically result in a $1 million settlement based mostly on HIPAA violations alone.
Assaults on staff’ digital units and identities are hovering
Healthcare CISOs inform VentureBeat that makes an attempt to steal staff’ digital units are hovering as a result of PHI data command the best costs on the darkish internet and are untraceable. The U.S. Division of Well being and Human Providers (HHS) Breach Portal exhibits that within the final eighteen months alone, 799 healthcare suppliers have been breached, 551 of them experiencing a server-based assault and 173 email-based wherein laptops have been used to realize entry.
CrowdStrike’s cofounder and CEO George Kurtz stated in his keynote ultimately yr’s Fal.Con that “80% of the assaults or the compromises that we see use some type of id and credential theft.”
The Id Outlined Safety Alliance (IDSA)’s 2023 Trends in Securing Digital Identities report discovered that 90% of organizations skilled no less than one identity-related breach up to now yr, representing a 7.1% improve year-over-year.
Preparing for automated assaults that weaponize AI at scale
Deepfake attacks are so pervasive that the Department of Homeland Security supplies the information Increasing Threats of Deepfake Identities, which outlines find out how to counter them. VentureBeat has discovered of a number of tried deepfake assaults on main enterprise software program CEOs that comply with the identical assault sample wherein Zscaler CEO Jay Chaudhyr’s voice was used to extort funds from the corporate’s India-based operations.
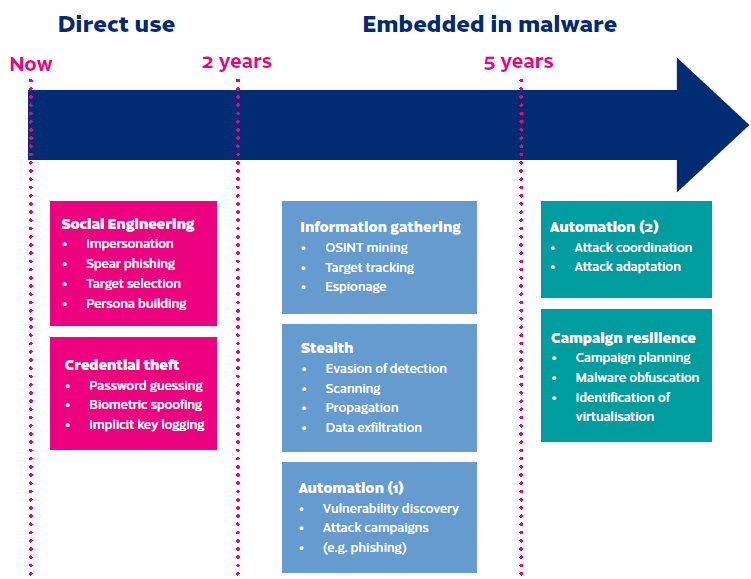
Chaudhry, Kurtz and CEOs of prime cybersecurity firms agree that stolen identities and privileged entry credentials are clients’ greatest threats. The Finnish Transport and Communications Company National Cyber Security Centre and WithSecure commissioned a research to foretell AI-enabled cyberattacks, as proven beneath.

How CISOs are utilizing AI to guard staff’ identities
Safety groups and the CISOs main them can’t afford to lose the AI warfare. The next 5 AI and machine studying (ML) methods have turn out to be desk stakes for stopping identity-based assaults:
Getting a extra exact rely, location and telemetry of all endpoints, machines and related identities
Cybersecurity and IT groups typically can’t find 35% to 40% of their endpoints and machines. With the proliferation of latest identities assigned to endpoints and the ensuing unchecked agent sprawl, attackers’ reconnaissance efforts rapidly discover over configured endpoints.
Endpoint sprawl makes id breaches tougher to cease. Six in 10 (59%) endpoints have no less than one id and entry administration (IAM) agent, and 11% have two or extra. These and different findings from Absolute Software’s 2023 Resilience Index illustrate the false sense of safety organizations have in safety instruments.
The Index discovered that many endpoint controls aren’t put in accurately, leaving 25 to 30% of units weak to assault. Treating each id as a brand new safety perimeter, implementing least privileged entry, monitoring each transaction and going all in on zero belief for each endpoint have to be a precedence.
Transferring past cell gadget VPNs and standardizing AI-enabled Cellular Risk Protection (MTD)
In a latest interview with VentureBeat, Ivanti chief product officer Srinivas Mukkamala famous that, “more and more, our cell telephones include our entire lives. On the coronary heart of recent gadget administration organizations [protecting] information in every single place work occurs, particularly work that’s taking place on private units.”
Mukkamala’s feedback replicate what VentureBeat hears from CISOs in healthcare, manufacturing and monetary providers, wherein cell units are steadily an assault goal.
Mukkamala suggested that “there’s a continued must extra simply management what info apps have entry to and keep away from granting inappropriate or extreme permissions, which places people and organizations in danger. IT and safety groups are more and more turning to automation and AI to ease the guide and mundane components of gadget administration and importantly, to create a moat across the private information and work information accessible via our telephones.”
Enhancing threat scoring accuracy and precision to extra rapidly determine id threats
CISOs and their groups inform VentureBeat they’ve supplied to assist check the newest technology of AI and ML-based risk-scoring fashions their suppliers are readying for launch. Main cybersecurity suppliers have already launched improved threat scoring to determine and thwart identity-based assaults.
AI is proving efficient in analyzing massive volumes of id and entry information in actual time to detect delicate patterns and anomalies that point out compromised credentials or insider threats. Adopting a real-time telemetry strategy reduces false positives.
Detecting artificial id fraud and deepfakes
From lowering false positives and figuring out artificial fraud to recognizing deepfakes, all AI-based id platforms and options share the widespread attributes of counting on many years of information to coach fashions and assigning belief scores by transaction.
For example, Telesign’s model-based strategy is noteworthy in its effectivity in getting probably the most worth from varied real-time telemetry information sources. Their mannequin depends on greater than 2,200 digital attributes and creates insights based mostly on roughly 5 billion distinctive cellphone numbers, greater than 15 years of historic information patterns and supporting analytics.
Cellphone quantity velocity, visitors patterns, fraud database consortiums and cellphone information attributes distinguish Telesign’s strategy. Id indicators are scored for anomalies which will point out an artificial id. The system “learns” from predictive analytics and supervised and unsupervised ML algorithms.
The corporate’s threat evaluation mannequin combines structured and unstructured ML to offer a threat evaluation rating in milliseconds, verifying whether or not a brand new account is respectable.

Counting on resilient, self-healing endpoints
Enabling self-healing endpoints to regenerate themselves autonomously and detect and reply to potential threats are two methods AI drives higher endpoint resilience. AI additionally permits endpoints to rapidly detect and reply to anomalies and superior threats that rules-based techniques miss.
CISOs inform VentureBeat that they use AI-based self-healing endpoints to scale back guide IT help time and value, enhance compliance and determine identity-based breach makes an attempt the place attackers attempt to acquire entry utilizing stolen privileged credentials.
Main self-healing endpoint suppliers embody Absolute, Akamai, Ivanti, Malwarebytes, Microsoft, SentinelOne, Tanium and Trend Micro. Absolute’s Resilience platform is noteworthy because it supplies real-time visibility and management of any gadget, whether or not on the community or not. Their platform is factory-embedded in firmware by 28 prime gadget producers, making it the world’s solely firmware-embedded endpoint visibility and management platform. Absolute is firmware embedded in additional than 600 million endpoints and the corporate serves 21,000 international clients.
AI is core to the way forward for id safety
As a latest CrowdStrike report illustrated, identities are beneath siege. Distant and hybrid employees are high-value targets as a result of attackers additionally need to steal their identities.
By prioritizing AI for 360-degree endpoint monitoring, multi-layered cell menace protection, real-time threat scoring, artificial fraud detection and self-healing endpoints, organizations can defend staff’ identities and scale back the specter of a breach.
AI-based platforms and techniques are proving efficient in figuring out anomalies and potential threats in actual time, in the end shutting down identity-based breaches and makes an attempt to make use of artificial identities and stolen entry credentials.