VentureBeat presents: AI Unleashed – An unique govt occasion for enterprise knowledge leaders. Hear from high business leaders on Nov 15. Reserve your free pass
Generative AI defines the way forward for id entry administration (IAM) by enhancing outlier habits evaluation, growing the accuracy of alerts and streamlining administrative duties whereas guarding in opposition to new threats.
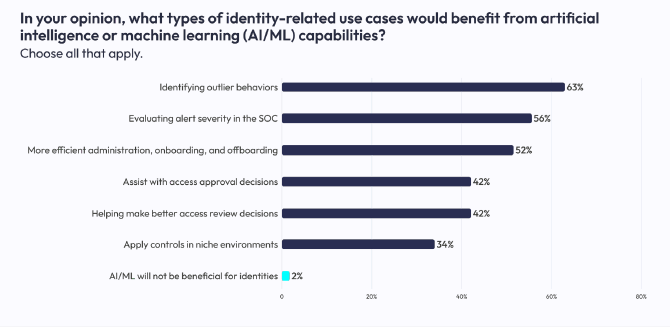
The bulk (98%) of safety professionals consider AI and machine studying (ML) can be helpful in combating identity-based breaches and consider it as a pivotal know-how in unifying their many id frameworks. Nicely over half (63%), predict AI’s main use case can be better accuracy in figuring out outlier habits. One other 56% consider AI will assist enhance the accuracy of alerts, and 52% consider AI will assist streamline administrative duties.
The Identification Outlined Safety Alliance’s latest report, 2023 Tendencies in Securing Digital Identities, additionally reveals how safety professionals are challenged to get various id frameworks from a number of distributors and totally different architectures to supply constant knowledge and insights.

Generative AI shrinks assault surfaces and expands the market
Insider threats and zombie credentials are two of essentially the most difficult assault surfaces to detect and cease an intrusion or breach try. Count on to see the main IAM suppliers undertake gen AI to create auto-deployed decoys, stepwise enhancements to behavioral detection and response, positive factors in Asset Graph know-how and fast-tracking enhancements to their prolonged detection and response (XDR) platforms.
Each IAM supplier has gen AI on their roadmap and is transferring shortly to ship new merchandise that capitalize on its potential to supply contextual intelligence. Main IAM suppliers embrace AWS, CrowdStrike, Delinea, Ericom, ForgeRock, Ivanti, Google Cloud Identity, IBM Cloud Identity, Microsoft Azure Active Directory, Palo Alto Networks and Zscaler.
The extra profitable gen AI is in shrinking assault surfaces, the extra its internet impact can be to develop the market. Gartner predicts the worldwide IAM market will enhance from $16.1 billion in 2023 to $24.9 billion in 2027. Broader end-user spending for the worldwide data safety and danger administration market will develop to $186 billion in 2023, with a relentless foreign money progress of 13.4%. The market will attain $289 billion in 2027, with a CAGR of 11.0% between 2022 to 2027.
Gen AI reveals the potential to shut gaps in cloud safety, the fastest-growing data safety and danger administration market that Gartner tracks. Cloud safety services are predicted to develop from $4.4 billion in 2022 to 12.8 billion in 2027, attaining a 23.5% compound annual progress charge (CAGR).
Software safety is predicted to develop from $5.7 billion in income this yr to $9.6 billion in 2027, attaining a 13.6% CAGR. International spending on zero-trust safety software program and options will develop from $27.4 billion in 2022 to $60.7 billion by 2027, attaining a CAGR of 17.3%.
Stepping up generative AI efforts in IAM
IAM suppliers must step up their efforts utilizing gen AI to establish and defeat the growing variety of malware-free assaults, which are sometimes mixed with convincing social engineering techniques. Attackers utilizing gen AI to create, launch and monitor malware-free intrusions accounted for 71% of all detections as listed by the CrowdStrike Threat Graph.
The newest Falcon Overwatch Threat Hunting Report illustrates how assault methods goal for identities first.
“A key discovering from the report was that upwards of 60% of interactive intrusions noticed by OverWatch concerned the usage of legitimate credentials, which proceed to be abused by adversaries to facilitate preliminary entry and lateral motion,” stated Param Singh, VP for Falcon OverWatch at CrowdStrike.
“Identification is the place safety goes and can revolve round going ahead as a result of there’s simply a lot extra wealthy knowledge there,” Ariel Tseitlin, a associate at Scale Venture Partners, advised VentureBeat earlier this yr. IAM jumped from eighth place to second on this yr’s funding priorities rating, reflecting growing market considerations about id safety in multicloud tech stacks.
In a latest collection of interviews, IAM suppliers and the CISOs they serve advised VentureBeat what they’re most is seeing how gen AI can assist shut the gaps their organizations face in reaching identity-first safety. IAM suppliers are attempting to unravel the gaps between id and endpoint safety, counting on gen AI and coaching fashions to bridge that hole with extra contextual intelligence.

The place IAM product leaders are focusing gen AI
CISOs have constantly advised VentureBeat that stopping an insider menace worries them and their groups essentially the most. Workers with authentic IDs — some with entry credentials and some with admin rights — are trusted and transfer freely by means of infrastructure to do their jobs.
Monitoring community actions and identities gained’t catch a breach utilizing stolen credentials or an insider assault. Moreover, attackers typically know the networks they’re attacking higher than the admins operating them, and the menace turns into much more extreme.
VentureBeat spoke with product leaders liable for the following era of IAM techniques to get their ideas on fixing this, and listed here are their observations.
Auditing all entry credentials in real-time to confirm entry privileges by useful resource
DropBox, Field and Microsoft Sharepoint have years of mental property, buyer information and transaction data uncovered as a result of credentials have by no means been audited or revoked. Product leaders throughout IAM suppliers say they see this typically of their clients’ networks, and it’s frequent for breaches to occur. No system catches them as a result of authentic credentials have been used.
Practically half (45%) of enterprises suspect former workers and contractors nonetheless have energetic entry to firm techniques and information, in accordance with a latest research by Ivanti.
Throughout an interview with VentureBeat, Srinivas Mukkamala, Ivanti CPO, stated that “giant organizations typically fail to account for the large ecosystem of apps, platforms and third-party providers that grant entry properly previous an worker’s termination.”
Mukkamala continued: “A surprisingly giant variety of safety professionals — and even leadership-level executives — nonetheless have entry to former employers’ techniques and knowledge.”
Behavioral evaluation for anomaly detection and response
Each IAM supplier has their anomaly detection resolution at the moment out there or of their second era of enhancing it with gen AI. It’s a powerful use case for the know-how, as it will probably establish uncommon entry patterns or potential breaches by analyzing giant datasets in real-time, considerably enhancing detection.
IAM product leaders say their roadmaps mirror broadening the usage of gen AI-based behavioral evaluation for fraud detection, endpoint safety, server and knowledge heart monitoring and extra. Main suppliers embrace CrowdStrike, CyberArk, Ivanti, Microsoft, Thales, Ping Identity and others.
Figuring out, isolating and stopping insider threats
Each IAM supplier that VentureBeat has had briefings with has an insider menace resolution already out there or on their roadmap. Their purpose is to make use of gen AI to fast-track insider menace options to extend the accuracy and reliability of alerts whereas sending out decoy containers, shares and belongings that an inside attacker would attempt to breach.
IAM product managers typically go to their clients and spend a day in Safety Operations Facilities (SOC) to see how alert workflows will be improved, particularly in insider threats.
Based on one main supplier, it’s a really efficient method, and so they’re productizing what they’ve discovered. Given this excessive precedence to the IAM supplier group, it’s cheap to imagine there can be acquisitions on this space in 2024. As an illustration, in 2022, CrowdStrike acquired Reposify to strengthen their exterior assault floor administration platform on Falcon, saying that the core know-how would additionally assist their buyer cease inside assaults.