Head over to our on-demand library to view classes from VB Remodel 2023. Register Right here
The extra built-in AI, automation and menace intelligence are throughout tech stacks and SecOps groups, the stronger they make an enterprise in opposition to breaches. Comply with-on advantages embody better cyber-resilience, and spending much less on information breaches than enterprises with no AI or automation defenses in any respect.
IBM Safety’s 2023 Cost of a Data Breach Report supplies compelling proof that investing in AI, automation and menace intelligence delivers shorter breach lifecycles, decrease breach prices and a stronger, extra resilient safety posture company-wide. The report relies on evaluation of 553 precise breaches between March 2022 and March 2023.
The findings are excellent news for CISOs and their groups, lots of whom are short-staffed and juggling a number of priorities, balancing help for brand spanking new enterprise initiatives whereas defending digital workforces. As IBM discovered, the typical whole price of an information breach reached an all-time excessive of $4.45 million globally, representing a 15% improve during the last three years. There’s the added strain to establish and comprise a breach quicker.
IBM’s Institute for Enterprise Worth examine of AI and automation in cybersecurity additionally finds that enterprises utilizing AI as a part of their broader cybersecurity technique consider gaining a extra holistic view of their digital landscapes. Thirty-five % are making use of AI and automation to find endpoints and enhance how they handle property, a use case they predict will improve by 50% in three years. Endpoints are the right use case for making use of AI to breaches due to the proliferating variety of new identities on each endpoint.
Why AI must be cybersecurity’s new DNA
Scanning public cloud cases for gaps in cloud safety (together with misconfigurations), inventing new malware and ransomware strains and utilizing generative AI and ChatGPT to fine-tune social engineering and pretexting assaults are only a few of the methods attackers attempt to evade being detected.
Cybercrime gangs and complicated advanced persistent threat (APT) teams actively recruit AI and machine learning (ML) specialists to design their Massive Language Fashions (LLM) whereas additionally in search of new methods to deprave mannequin information and invent malware able to evading the present era of menace detection and response techniques beginning with endpoints.
CISOs want AI, ML, automation and menace intelligence instruments in the event that they’re going to have an opportunity of staying at aggressive parity with attackers. IBM’s report supplies compelling proof that AI is delivering outcomes and must be the brand new DNA of cybersecurity.
Integrating AI and automation diminished the breach lifecycle by 33% or 108 days
IBM discovered that enterprises that superior their integration of AI and automation into SecOps groups to the platform stage are lowering breach lifecycles by one-third, or 108 days. That’s a major drop from a mean of 214 days. The typical breach lasts 322 days when a company isn’t utilizing AI or automation to enhance detection and response.
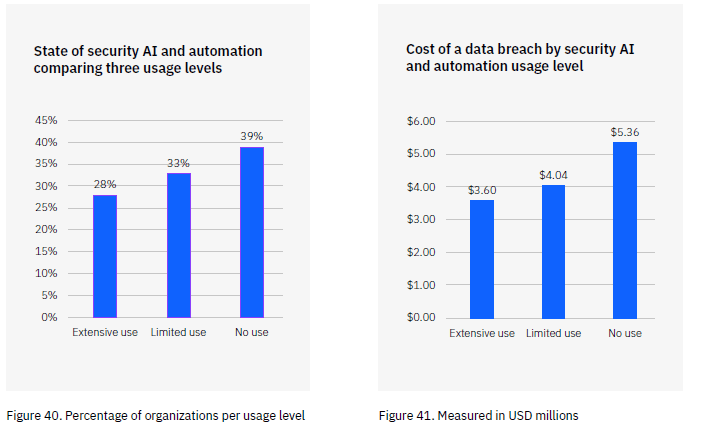
Intensive use of AI and automation resulted in 33.6% price financial savings for the typical information breach.
Integrating AI and automation throughout a tech stack to realize visibility, detection and obtain real-time response to potential intrusions and breaches pays off. Organizations with no AI or automation in place to establish and act on intrusions and seashores had a mean breach price of $5.36 million.
Enterprises with in depth AI and automation integration supporting their SecOps groups, tech stack and cyber-resilience methods skilled far cheaper breaches. The typical price of a breach with in depth AI and automation in place averaged $3.6 million. That’s a compelling sufficient price financial savings to construct a enterprise case round.

Regardless of the benefits, simply 28% of enterprises are extensively integrating AI and automation
Given the beneficial properties AI and automation ship, it’s stunning that almost one-third of enterprises surveyed have adopted these new applied sciences. IBM’s workforce additionally discovered that 33% had restricted use throughout only one or two safety operations. That leaves 4 in 10 enterprises counting on present and legacy era techniques that attackers have fine-tuned their tradecraft to evade.
In one other examine, 71% of all intrusions listed by CrowdStrike Threat Graph have been malware-free. Attackers rapidly capitalize on any hole or weak point they uncover, with privileged entry credentials and identities being a main goal, a key analysis discovering from CrowdStrike’s Falcon OverWatch Threat Hunting Report. Attackers more and more use AI to evade detection and are centered on stealing cloud identities, credentials and information, in line with the report. This additional exhibits the necessity for clever AI-driven cybersecurity instruments.
Gartner’s 2022 Innovation Insight for Assault Floor Administration report predicts that by 2026, 20% of corporations (versus 1% in 2022) could have a excessive stage of visibility (95% or extra) of all their property, prioritized by threat and management protection. Gartner contends that cyber asset assault floor administration (CAASM) is important to convey an built-in, extra unified view of cyber property to SecOps and IT groups, CAASM stresses the necessity for integration at scale with secured APIs.
IBM’s examine exhibits that SecOps groups are nonetheless shedding the AI battle.
Nearly all of SecOps groups are nonetheless counting on guide processes and have but to undertake automation or AI considerably, in line with the report. There’s a main disconnect between executives’ intentions for adopting AI to enhance cybersecurity and what’s occurring.
Ninety-three % of IT executives say they’re already utilizing or contemplating implementing AI and ML to strengthen their cybersecurity tech stacks, whereas 28% have adopted these applied sciences. In the meantime, attackers are efficiently recruiting AI, ML and generative AI specialists who can overwhelm an assault floor at machine velocity and scale, launching the whole lot from DDOS to utilizing living-off-the-land (LOTL) techniques that depend on Powershell, PsExec, Home windows Administration Interface (WMI) and different frequent instruments to keep away from detection whereas launching assaults.
“Whereas extortion has principally been related to ransomware, campaigns have included quite a lot of different strategies to use strain on their targets,” writes Chris Caridi, cyber menace analyst for IBM Safety Menace Intelligence. “And these embody DDoS assaults, encrypting information, and extra not too long ago, some double and triple extortion threats, combining a number of of the beforehand seen parts.”
This also needs to be thought-about with the proliferation of deepfakes. Zscaler CEO Jay Chaudhry was the latest goal of a deep faux assault. Chaudhry informed the viewers at Zenith Stay 2023 about one latest incident by which an attacker used a deepfake of his voice to extort funds from the corporate’s India-based operations.
In a recent interview, Chaudhry mentioned, “This was an instance of the place they [the attackers] really simulated my voice, my sound … increasingly impersonation of sound is occurring, however you’ll [also] see increasingly impersonation of appears to be like and feels.” Deepfakes have change into so commonplace that the Department of Homeland Security has issued the information Increasing Threats of Deepfake Identities.
AI discovers anomalies at scale and machine-level speeds
AI and automation ship measurable leads to bettering safety personalization whereas imposing least privileged entry. SecOps groups with an built-in AI and automation tech stack are quicker at figuring out and taking motion on anomalies that might point out an intrusion or breach.
AI and ML excel at analyzing huge volumes of system and consumer exercise information that energy menace intelligence techniques. IBM discovered that when a menace intelligence system has real-time information analyzed by AI and ML algorithms, the time to establish a breach is diminished by 28 days on common.
Breaches price much less if SecOps groups discover them first
AI additionally pays off by serving to SecOps groups establish the breach themselves versus ready for an attacker to announce the break or having legislation enforcement inform them. When SecOps groups can establish the breach, they save practically $1 million. The examine additionally in contrast mean-time-to-identify (MTTI) and mean-time-to-contain (MTTC), discovering that in depth integration of AI and automation diminished each.

Preserve AI, automation, and menace intelligence within the context of zero belief
Zero belief assumes a breach has already occurred, and each menace floor must be frequently monitored and secured. Because the IBM examine exhibits, AI, ML and automation are proving efficient in offering real-time menace intelligence.
Throughout a latest interview with VentureBeat, zero belief creator John Kindervag suggested that “you begin with a shield floor. I’ve, and in case you haven’t seen it, it’s known as the zero-trust learning curve. You don’t begin with know-how, and that’s the misunderstanding of this. After all, the distributors need to promote the know-how, so [they say] it is advisable to begin with our know-how. None of that’s true. You begin with a shield floor, after which you determine [the technology].”
Kindervag’s recommendation is nicely taken and displays how efficient AI, ML, automation and menace intelligence will be deployed and ship outcomes at scale. Saved in a zero belief context of defending one menace floor at a time, as Kindervag advises, these applied sciences ship worth.